Introduction
Proofpoint Inc., a frontrunner in cybersecurity and compliance, has announced its definitive agreement to acquire Illusive, a pioneer in Identity Threat Detection and Response (ITDR). With the acquisition set to close by January 2023, Proofpoint aims to strengthen its threat and information protection platforms by incorporating proactive identity risk discovery, remediation, and post-breach defense capabilities, creating a comprehensive solution for critical threats such as ransomware and data breaches.
The Growing Challenge of Identity-Based Attacks
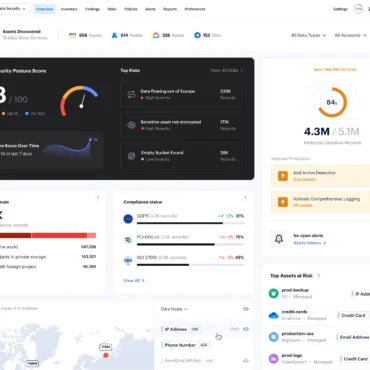
The global surge in cyberattacks has prompted threat actors to shift their focus towards identity-based attacks, resulting in 84% of organizations experiencing an identity-related breach in the past year. These attacks exploit identities through various means, such as privilege escalation, lateral movement, and abuse of Active Directory and cloud environments like Microsoft 365.
The Illusive Advantage
Integrating Illusive into Proofpoint’s platform will provide enterprises with unrivaled insights into the attacked and vulnerable identities across their organization, empowering them to better protect their Very Attacked People (VAPs). Illusive’s innovative solutions are trusted by leading multinational corporations to safeguard some of the world’s most renowned brands by denying attackers the privileged account access they need to execute their crimes.
A Shared Vision for Comprehensive Identity Security
The acquisition highlights Proofpoint’s commitment to innovation and growth, as well as its dedication to making it increasingly difficult for threat actors to succeed. Illusive’s founder and CEO, Ofer Israeli, expressed enthusiasm about joining forces with Proofpoint and contributing their unique ITDR approach to Proofpoint’s people-centric security vision.
Together, Proofpoint and Illusive will offer a comprehensive identity security suite as part of Proofpoint’s threat protection platform, featuring:
- Illusive Spotlight™: An agentless approach for automatic discovery and remediation of identity vulnerabilities before attackers can exploit them, providing unmatched visibility into vulnerable identities by scanning directory structures, privileged access management solutions, endpoints, servers, and services.
- Illusive Shadow™: A detection and response solution for identity threats that thwarts privilege escalation and lateral movement to critical assets, with an agentless architecture that prevents attacker detection and remains undefeated in over 150 red team exercises. This enables organizations to accelerate threat detection based on attacker interaction with deceptions, rather than relying on signatures or behaviors.
As the cyber threat landscape continues to evolve, this strategic acquisition positions Proofpoint and Illusive at the forefront of identity security, offering enterprises a powerful, unified solution to defend against the ever-growing menace of ransomware and data breaches.
Innocom is committed to providing its customers with enhanced discovery, detection, and response capabilities. By leveraging the cutting-edge solutions offered by Proofpoint and Illusive, Innocom empowers organizations to proactively identify and remediate identity vulnerabilities, effectively detect identity-based threats, and respond rapidly to protect critical assets. With a customer-centric approach and an unwavering focus on innovation, Innocom works closely with its clients to deliver comprehensive and tailored cybersecurity solutions that address today’s ever-evolving threat landscape, ensuring the safety and security of their digital ecosystems.
Read more about Application Delivery for Kubernetes
Read more about Secure application delivery